No concrete evidence was used to attribute the hack to Russia in June, just as no concrete evidence has been made available to attribute the hack to Iran now. However, the assignment of blame to these nation states coincided with other geopolitical issues pitting Russia and Iran against U.K. or U.S. interests.
On October 13, President Donald Trump – as anticipated – decertified the Joint Comprehensive Plan of Action (JCPOA), also known as the Iran nuclear accord, despite the fact that Iran was in full compliance with the agreement. Trump’s unilateral decision to put the survival of the deal in jeopardy was met with strong opposition by European leaders — including Germany, the United Kingdom, and France, whose leaders issued a joint statement condemning the move.
Interestingly, a day later, accusations conveniently emerged blaming the Iranian government for a June cyberattack that had targeted numerous U.K. politicians. The attackers allegedly sought to gain access to accounts of some members of parliament — all of which were protected by “weak passwords” — and were successful in some instances.
The evidence for blaming Iran was based solely on an “unpublished assessment by British intelligence” that was reported on by The London Times, though they merely disclosed the existence of the report and did not read it. Thus, its contents are unknown, as are its reasons for blaming the Iranian government. Despite that, the Times called the hack “Iran’s first significant act of cyberwarfare on Britain.” It also noted that the Trump administration “is likely to seize on the attack as proof that Mrs. May and other signatories to the deal are being naive in their dealings with Tehran.”
The cyberattack had previously been blamed on the Russian government. At the time, British intelligence had based this accusation on merely the belief “that responsibility for the attack is more likely to lie with another state rather than a small group of individual hackers,” as well as its assumption that “the number of states who might mount such an attack on the U.K. is limited, and, in addition to Russia, includes North Korea, China and Iran.” British intelligence had also noted that the identity of the hackers could prove impossible to establish with “absolute certainty.”
The decision to blame Russia came on the heels of France blaming Russia for the hack of Emmanuel Macron’s campaign data – which was later proven to not have involved Russia in any respect – and after the U.S. government had claimed that Russia was trying to interfere with the U.K. general election last June, another assertion that failed to hold water.
In other words, no concrete evidence was used to attribute the hack to Russia in June, just as no concrete evidence has been made available to attribute the hack to Iran now. However, the assignment of blame to these nation states coincided with other geopolitical issues pitting Russia and Iran against U.K. or U.S. interests.
As the Guardian noted, the assessment’s release comes as the U.S.’ and the U.K.’s public stances on the fate of the Iran deal could not be more different. However, the timing of this recent accusation looks much less coincidental when viewed in light of a plan of action considered by the Trump administration in dealing with potential diplomatic fallout from a unilateral decision to certify the Iran nuclear accord.
The plan — written by notorious neo-conservative John Bolton, who was very nearly Trump’s pick for Secretary of State — calls for, in part, “a diplomatic and public education effort to explain a decision not to certify and to abrogate the JCPOA.”
It adds that the U.S. government, as a part of this effort, “can bolster the case for abrogation by providing new, declassified information on Iran’s unacceptable behavior around the world.” It further notes that “this effort could well leak to the press.” The so-called “Bolton plan” also called for “early, quiet consultations with key players” in the U.K., among other nations involved in the nuclear accord.
While there is no hard evidence to link the Bolton plan to the emergence of these latest hacker accusations, the roadmap laid out by the Bolton plan and the time of publication suggest that the rise of the “Iranian hacker” in lieu of the “Russian hacker” is part of the U.S.’ broader approach in fomenting support for its decision to call the nuclear deal into question among its European allies.
Fog of cyberspace makes blame narratives easy to spin
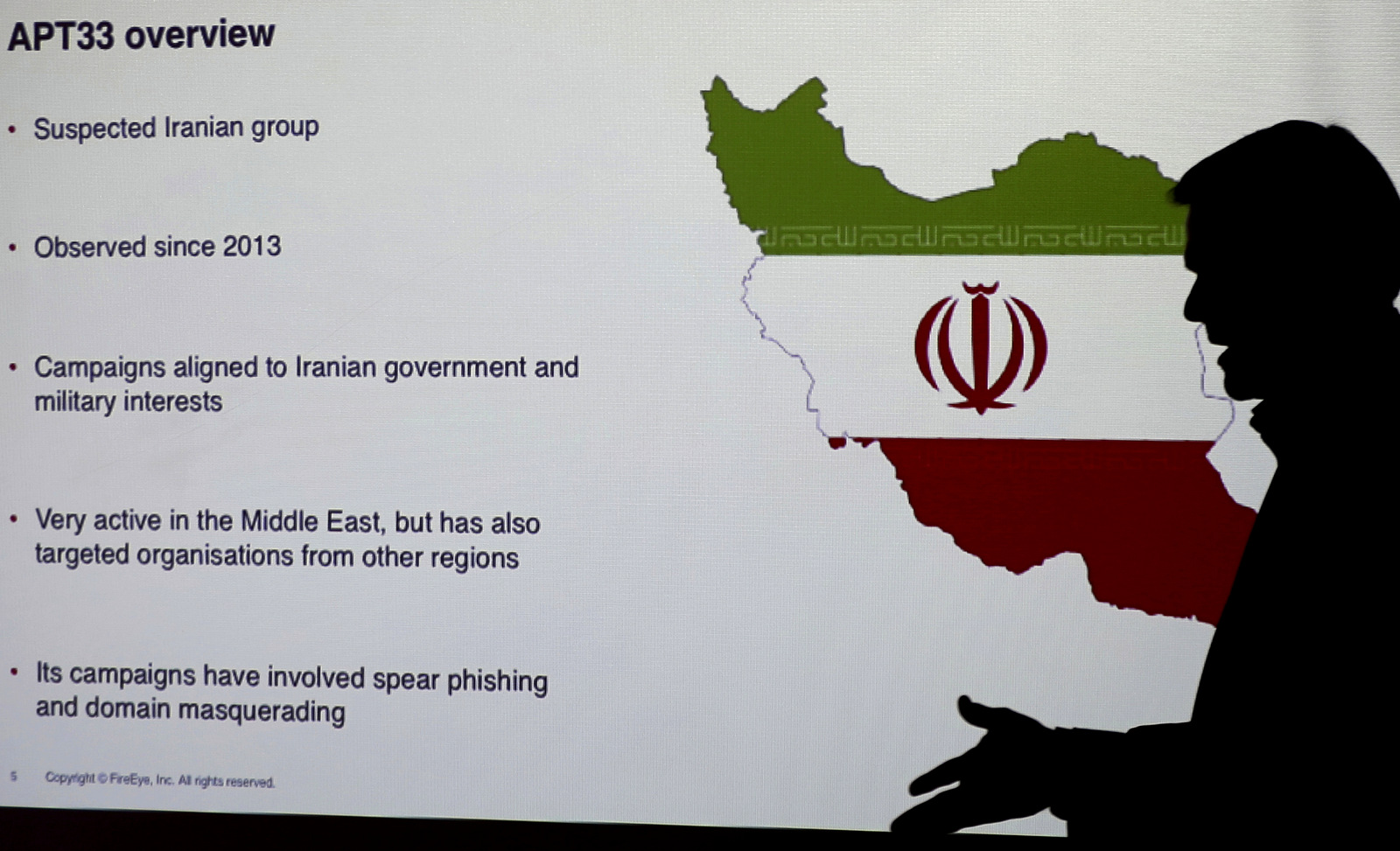
This is hardly the first time that an Iranian hacker narrative has been spun and used to call the nuclear accord into the question. Since the deal was reached, stories of Iranian hackers targeting the U.S. have cropped up, which subsequently have been used by opponents of the deal to argue that the Iranian government is seeking to undermine a deal from which it greatly benefits.
For instance, four months after the deal was signed, The New York Times published a piece on a hack of State Department employee social media accounts allegedly perpetrated by the Iranian government. The article asserts that Iran, which was blamed solely on the basis of statements by anonymous government officials, uses cyberespionage as “a tool to seek the kind of influence that some hard-liners in Iran may have hoped its nuclear program would eventually provide” — essentially equating the country’s nuclear program to its alleged and unproven cyberespionage activities.
Less than a year later, Iranian hackers were again accused by the U.S. of having hacked a small dam in New York state. Though the hack was never linked to the Iranian government, Senator Chuck Schumer (D-NY) blamed Tehran and called the attacks “malignant” and indicative of a threat that “could be metastasizing.”
Even when the link to the Iranian government failed to emerge, The Washington Post quoted James Lewis, a cybersecurity expert with the neo-conservative Center for Strategic and International Studies (CSIS) as saying the following: “There’s no such thing as a freelance hacker in Iran. They’re all connected to the state.” In other words, Lewis asserts that in Iran – a nation of 80 million people – a hacker independent of the state could not exist. Lewis also told the Post that Iran “may be receiving help from Russian hackers affiliated with the Kremlin” — another claim he asserted without evidence.
In addition, the Iranian hacker narrative — much like similar accusations leveled against Russia, North Korea or China — has been based on the assumption that only “rivals” of Western nations are to blame for cyberattacks. As seen with the U.K. cyberattack in June, British intelligence – after admitting that attribution of blame would most likely be impossible – assumed that Russia was responsible due to the “Russian hacker” hysteria evident at that time. However, nation states such as the United States or Israel – which have been shown to hack and spy on their allies on several occasions – are never included in the list of potential culprits.
In fact, these two nations have worked together to produce advanced cyberweapons such as the Stuxnet virus, which was used to sabotage Iran’s civilian nuclear power plants until its discovery in 2010. However, it later emerged that Stuxnet was the tip of the iceberg, as the U.S. had planned to target Iran’s air defenses, communications systems, and key parts of its power grid with cyberweapons in the event that the Iran nuclear accord failed to be agreed upon.
It has become increasingly evident that any nation state can be conveniently assigned blame for a cyberattack by agencies of Western governments — without evidence and in the service of broader geopolitical goals. Such governments have hitherto had no problem having their evidence-free claims amplified by a compliant press.
As the Russia hacker/meddler narrative continues to collapse, Iran seems poised to become the new boogeyman of Western governments. Such a shift will be welcomed by those seeking not only to destroy the Iran nuclear accord but to initiate a full-scale war against the Islamic Republic.
Source: www.mintpressnews.com




