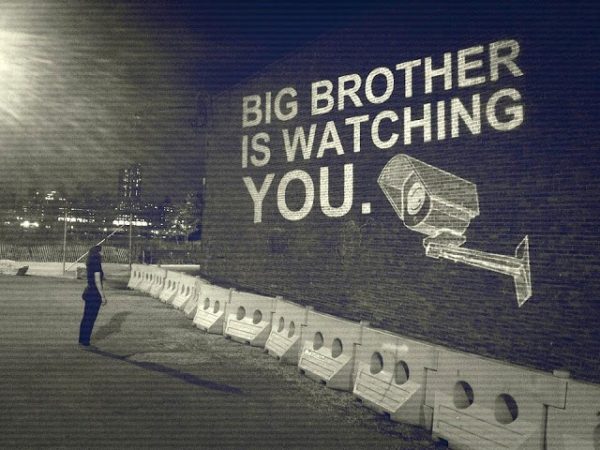
“We are rapidly entering the age of no privacy, where everyone is open to surveillance at all times; where there are no secrets from government.” William O. Douglas, Supreme Court Justice (1966)
The government has become an expert in finding ways to sidestep what it considers “inconvenient laws” aimed at ensuring accountability and thereby bringing about government transparency and protecting citizen privacy.
Indeed, it has mastered the art of stealth maneuvers and end-runs around the Constitution.
It knows all too well how to hide its nefarious, covert, clandestine activities behind the classified language of national security and terrorism. And when that doesn’t suffice, it obfuscates, complicates, stymies or just plain bamboozles the public into remaining in the dark.
Case in point: the National Security Agency (NSA) has been diverting “internet traffic, normally safeguarded by constitutional protections, overseas in order to conduct unrestrained data collection on Americans.”
It’s extraordinary rendition all over again, only this time it’s surveillance instead of torture being outsourced.
In much the same way that the government moved its torture programs overseas in order to bypass legal prohibitions against doing so on American soil, it is doing the same thing for its surveillance programs.
By shifting its data storage, collection and surveillance activities outside of the country—a tactic referred to as “traffic shaping” —the government is able to bypass constitutional protections against unwarranted searches of Americans’ emails, documents, social networking data, and other cloud-stored data.
The government, however, doesn’t even need to move its programs overseas. It just has to push the data over the border in order to “[circumvent] constitutional and statutory safeguards seeking to protect the privacy of Americans.”
No wonder the NSA appeared so unfazed about the USA Freedom Act, which was supposed to put an end to the NSA’s controversial collection of metadata from Americans’ phone calls. The NSA had already figured out a way to accomplish the same results (illegally spying on Americans’ communications) without being shackled by the legislative or judicial branches of the government.
Mind you, this metadata collection now being carried out overseas is just a small piece of the surveillance pie.
The government and its corporate partners have a veritable arsenal of surveillance programs that will continue to operate largely in secret, carrying out warrantless mass surveillance on hundreds of millions of Americans’ phone calls, emails, text messages and the like, beyond the scrutiny of most of Congress and the taxpayers who are forced to fund its multi-billion dollar secret black ops budget.
In other words, the surveillance state is alive and well and kicking privacy to shreds in America.
On any given day, the average American going about his daily business is monitored, surveilled, spied on and tracked in more than 20 different ways by both government and corporate eyes and ears.
Whether you’re walking through a store, driving your car, checking email, or talking to friends and family on the phone, you can be sure that some government agency, whether the NSA or some other entity, is listening in and tracking your behavior. This doesn’t even begin to touch on the corporate trackers that monitor your purchases, web browsing, Facebook posts and other activities taking place in the cyber sphere.
We have now moved into a full-blown police state that is rapidly shifting into high-gear under the auspices of the surveillance state.
Not content to merely transform local police into extensions of the military, the Department of Homeland Security, the Justice Department and the FBI are working to turn the nation’s police officers into techno-warriors, complete with iris scanners, body scanners, thermal imaging Doppler radar devices, facial recognition programs, license plate readers, cell phone Stingray devices and so much more.
Add in the fusion centers, city-wide surveillance networks, data clouds conveniently hosted overseas by Amazon and Microsoft, drones equipped with thermal imaging cameras, and biometric databases, and you’ve got the makings of a world in which “privacy” is reserved exclusively for government agencies.
Thus, the NSA’s “technotyranny” is the least of our worries.
Just about every branch of the government—from the Postal Service to the Treasury Department and every agency in between—now has its own surveillance sector, authorized to spy on the American people.
And of course that doesn’t even begin to touch on the complicity of the corporate sector, which buys and sells us from cradle to grave, until we have no more data left to mine. Indeed, Facebook, Amazon and Google are among the government’s closest competitors when it comes to carrying out surveillance on Americans, monitoring the content of your emails, tracking your purchases, exploiting your social media posts and turning that information over to the government.
It’s not just what we say, where we go and what we buy that is being tracked.
We’re being surveilled right down to our genes, thanks to a potent combination of hardware, software and data collection that scans our biometrics—our faces, irises, voices, genetics, even our gait—runs them through computer programs that can break the data down into unique “identifiers,” and then offers them up to the government and its corporate allies for their respective uses.
All of those internet-connected gadgets we just have to have (Forbes refers to them as “(data) pipelines to our intimate bodily processes”) are setting us up for a brave new world where there is nowhere to run and nowhere to hide.
Incredibly, there are still individuals who insist that they have nothing to fear from the police state and nothing to hide from the surveillance state, because they have done nothing wrong.
To those sanctimonious few, secure in their delusions, let this be a warning.
There is no safe place and no watertight alibi.
The danger posed by the American police/surveillance state applies equally to all of us.
As I make clear in my book Battlefield America: The War On The American People, in an age of too many laws, too many prisons, too many government spies, and too many corporations eager to make a fast buck at the expense of the American taxpayer, we are all guilty of some transgression or another.
Eventually, we will all be made to suffer the same consequences in the electronic concentration camp that surrounds us.
Authored by John Whitehead via The Rutherford Institute